Why you need a Vulnerability Scanning Service
Most breaches exploit known, preventable weaknesses. Yet for many organisations, vulnerability management remains reactive, inconsistent, or simply deprioritised under the pressure of day-to-day operations. Attackers count on that gap.
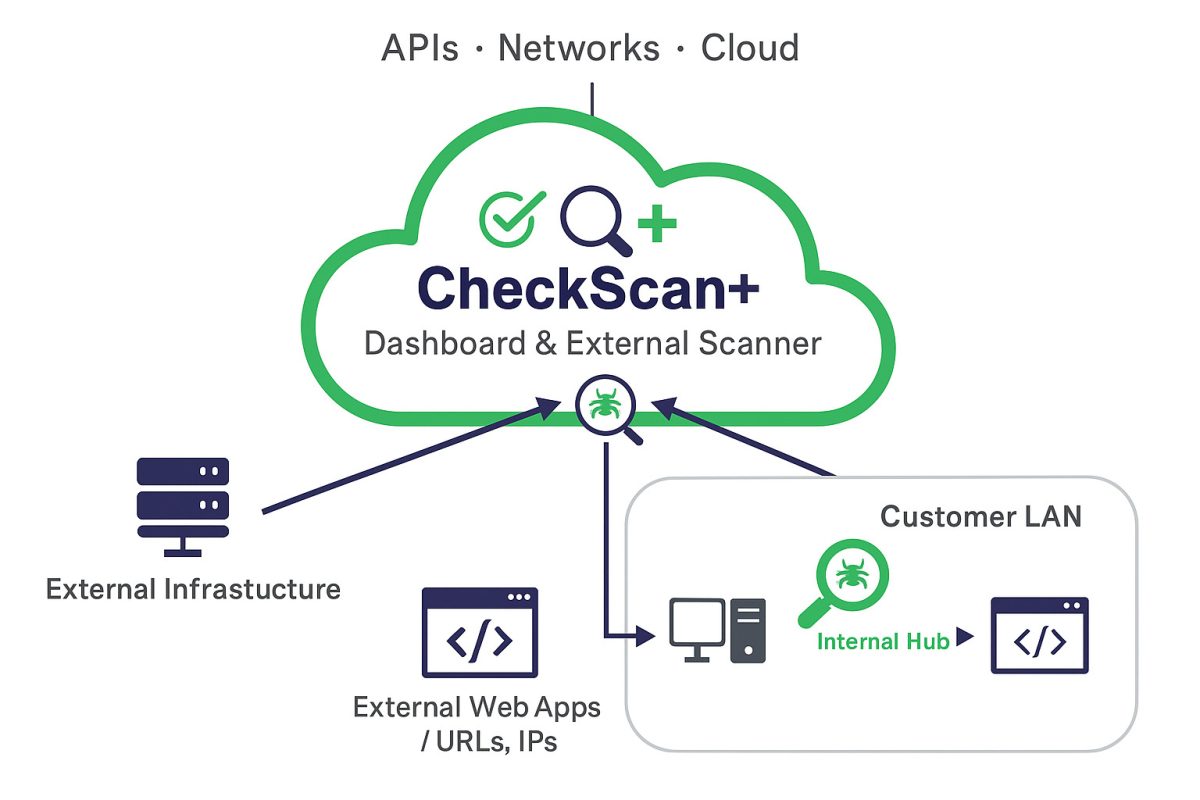
CheckScan+ closes it. Our managed vulnerability scanning service regularly scans your network, websites, web applications, APIs, and cloud environments, then delivers a clear, prioritised action plan your team can act on immediately. Not an overwhelming list of hundreds of findings that never get resolved. You will know exactly what needs fixing, why it matters, and how to address it. And because CheckScan+ produces compliance-ready documentation aligned to NIS2, DORA, ISO 27001, PCI DSS, and GDPR, it strengthens your security posture and supports your regulatory obligations at the same time.
85%of successful breaches exploit known vulnerabilities that had a patch available for over a year. The risk is not unknown. It is unmanaged.
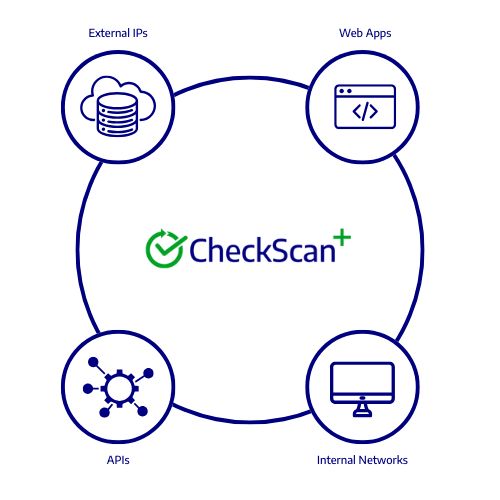
What we scan
CheckScan+ scans your full attack surface:
- External websites and web applications
- APIs and integrations
- Internal networks and IPs
- Cloud services
- Public-facing infrastructure (URLs, domains, servers)
Whether you run a small network or manage complex hybrid estates, CheckScan+ delivers continuous, accurate visibility where it counts.
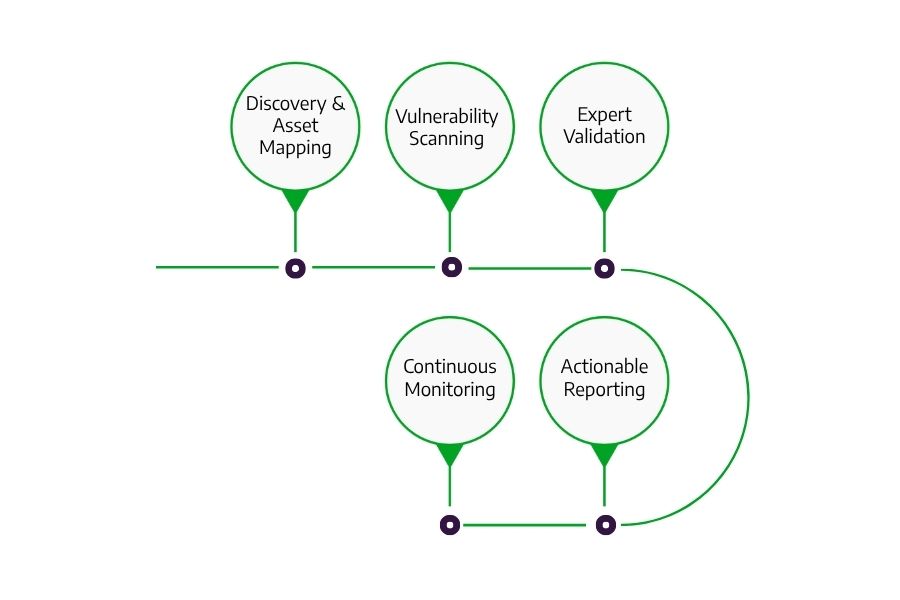
How CheckScan+ Works
CheckScan+ is more than just scanning. It’s a continuous, expert-led process designed to uncover real risks, prioritise what matters, and guide your team with clear next steps. So nothing critical slips through the cracks.
- Discovery & Asset Mapping
We map your environment, including external web apps, APIs, networks, cloud services, and infrastructure. - Vulnerability Scanning
Our scanning engine mimics real-world attack behaviour—testing for XSS, SQLi, IDOR, SSRF, privilege escalation, and more. - Expert Validation
Our analysts triage results, eliminate false positives, and focus your attention on real, exploitable issues. - Actionable Reporting
We give you a clean, prioritised action plan that’s easy to digest and ready for remediation. - Continuous Monitoring
Scans can be scheduled or triggered as needed—perfect for DevOps, CI/CD, or post-remediation validation.
Benefits of CheckScan+
Comprehensive Coverage
Scan your entire environment: networks, cloud workloads, external web apps, APIs, URLs, IPs, and source code.
Deep and Accurate Detection
Identify genuine risks without the noise. Our advanced scanning engine detects vulnerabilities across technologies and frameworks.
Effortless Usability
From simple setup to intuitive dashboards, CheckScan+ makes vulnerability management accessible, even for lean security teams.
Actionable Reporting
Clear, prioritised reports show exactly what needs fixing, why it matters, and how to resolve it, step by step.
DevSecOps Integration
Embed scanning into CI/CD pipelines. Run automated security checks with SAST and DAST capabilities to protect every release.
Flexible Scheduling
Run one-off scans, schedule them regularly, or trigger on-demand assessments whenever you deploy changes.
Recent Client Feedback
Continous Vulnerability Scanning Across Your Whole Stack
CheckScan+ goes beyond basic scanning to give you continuous visibility across your attack surface:
-
Dynamic Application Security Testing (DAST)
Simulate real-world attacks on your live applications. -
API and Cloud Security
Discover hidden risks in integrations and cloud services. -
External Attack Surface Management
Map and monitor public-facing assets to stay ahead of threats.
Clients who trust us
Why It’s Different
Not Just Tools – Real Security Analysts
We do not send raw scan data and leave you guessing. Every result is reviewed and validated by our vulnerabilities team, so you can trust what’s flagged.
Prioritisation That Saves Time
We know your team is stretched. That’s why we highlight high-risk and critical vulnerabilities first, so your efforts go where they have the greatest impact.
No False Sense of Security
Many scanners deliver alerts. We deliver clarity. With authenticated crawling, dynamic testing, and exploit validation, we reveal vulnerabilities that traditional tools miss, like logic flaws, exposed APIs, and misconfigurations.
What You Get
-
Managed vulnerability scanning—internal and external
-
Unlimited scan frequency
-
Continuous monitoring
-
Prioritised reporting with expert validation
-
False positive removal
-
Clear remediation guidance
-
Compliance-ready documentation (PCI DSS, NIS2, ISO 27001, GDPR, SOC2 etc)
-
Integration options for Jira, ticketing systems, and reporting tools
-
Support from our vulnerability team
FAQ's
What can I scan with CheckScan+?
You can scan networks, cloud environments, web applications, APIs, URLs, IPs, and source code for a comprehensive view of your vulnerabilities.
How easy is it to get started?
Setup is quick and straightforward. Our team will guide you through configuration so you can start scanning right away.
How do I use CheckScan+ with my development pipelines?
You can embed automated scans into your CI/CD workflows, running DAST checks as part of your build and release process.
What do the reports include?
You receive clear, prioritised reports with detailed findings and practical remediation advice to help you close security gaps efficiently.
How often should I scan?
We recommend continuous or scheduled scans, plus on-demand assessments when you deploy new assets or make significant changes. Scans can be scheduled weekly, bi-monthly, monthly, quarterly etc.
What is the difference between a manual penetration test and CheckScan+?
A manual penetration test involves security professionals simulating real-world attacks to find vulnerabilities that automated tools may miss. It is typically conducted at a specific point in time. CheckScan+ is a continuous vulnerability scanning service that automatically detects known issues across your environment. Many organisations use both approaches together—regular scanning to maintain baseline security, and periodic penetration tests for deeper assessment.
How does CheckScan+ handle false positives?
CheckScan+ is designed to minimise false positives with advanced detection logic and validation checks. Our Security Analysts will review and confirm findings with you. This helps ensure you focus your time on genuine risks rather than unnecessary noise.