Complete Automated Security Testing & Vulnerability Scanning
TL;DR: Continuous, automated vulnerability scanning that gives you up-to-the-minute security coverage across your entire IT estate, without slowing down your teams.
Always-On Vulnerability Coverage for Your Entire Environment
Modern attack surfaces change daily. New code, new assets, new exposures. Traditional point-in-time scans can’t keep up.
AppCheck from CommSec provides continuous, automated security testing that identifies vulnerabilities across your full environment, applications, infrastructure, networks, and cloud, so you always know where you stand.
No guesswork. No blind spots. Just current, actionable risk visibility.

What AppCheck Does
AppCheck is a fully automated vulnerability scanning platform designed to:
-
Continuously scan your entire digital estate
-
Detect known and emerging vulnerabilities as soon as they appear
-
Prioritise issues based on real-world exploitability
-
Provide clear remediation guidance for faster fixes
The result: security teams stay ahead of attackers instead of reacting after incidents occur.
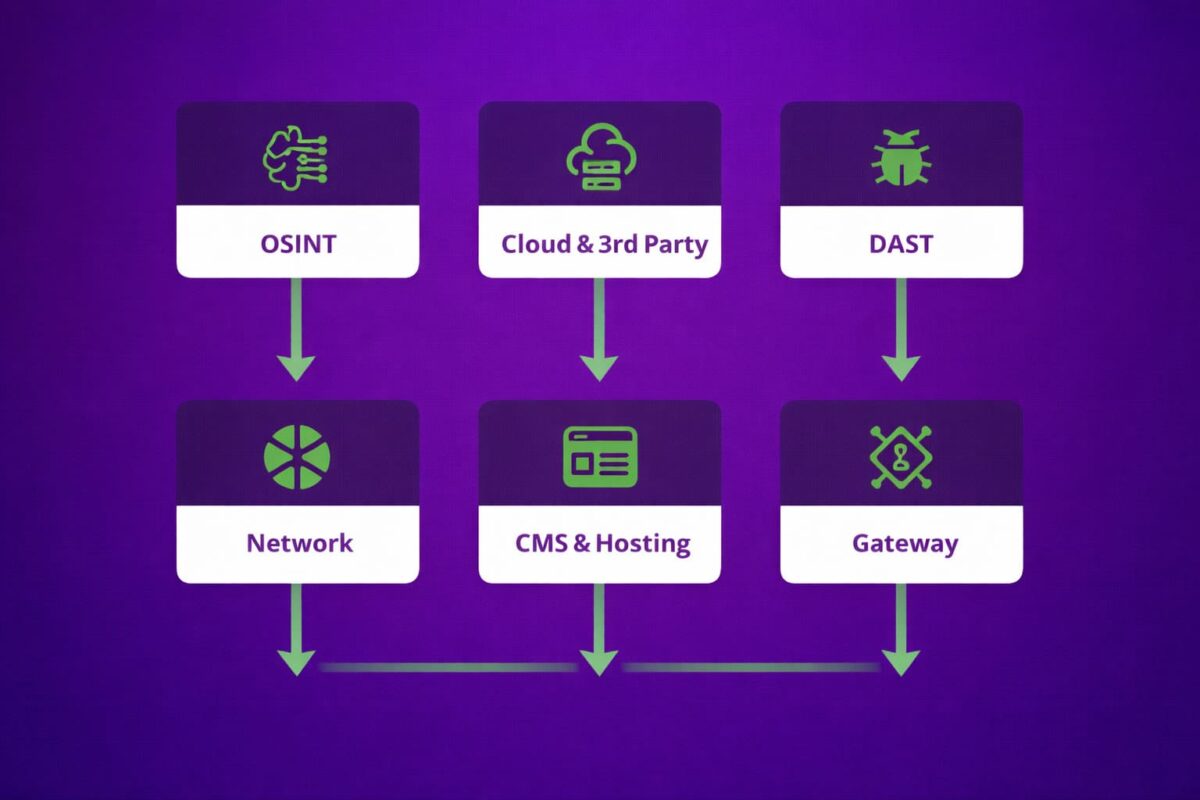
What We Scan
AppCheck delivers comprehensive coverage across:
-
Web applications (including OWASP Top 10 risks)
-
Internal and external networks
-
Cloud environments
-
APIs and internet-facing services
-
Infrastructure and operating systems
As your environment changes, scanning coverage updates automatically—ensuring nothing is missed.
Why Continuous Automated Scanning Matters
Threat actors don’t wait for quarterly assessments. Neither should you.
With AppCheck, you benefit from:
-
Up-to-the-minute vulnerability intelligence
Newly disclosed CVEs and attack techniques are incorporated as they emerge. -
Reduced attack surface
Identify and remediate exposures before they can be exploited. -
Lower operational overhead
Automated testing removes the need for constant manual scanning. -
Improved compliance readiness
Maintain ongoing evidence for standards such as ISO 27001, PCI DSS, and GDPR.
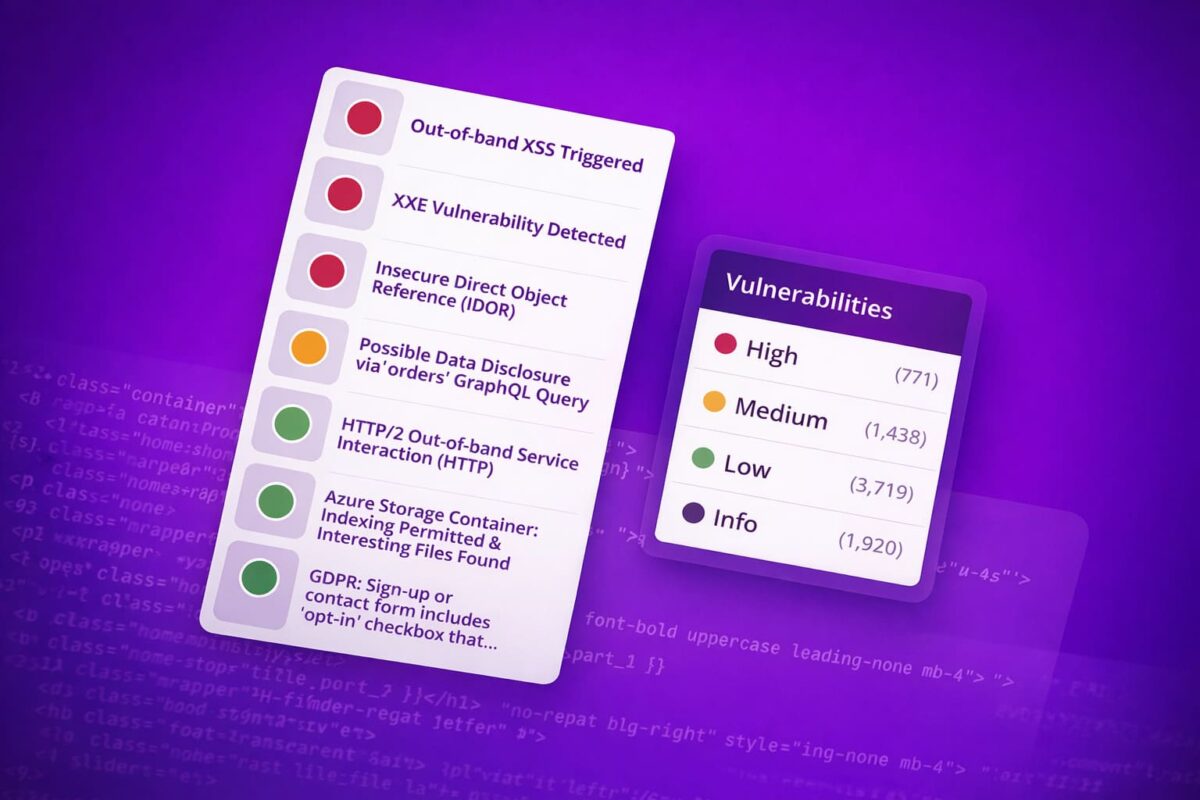
Clear Results, Not Just Alerts
AppCheck doesn’t overwhelm you with noise.
You get:
-
Risk-ranked findings based on severity and exploit likelihood
-
Plain-English explanations of each vulnerability
-
Practical remediation steps your teams can act on immediately
-
Centralised reporting across your entire estate
This makes AppCheck suitable for both security specialists and technical teams responsible for fixing issues.
Who This Service Is For
AppCheck is ideal for organisations that need continuous security visibility, including:
-
Businesses with complex or fast-changing IT environments
-
Organisations adopting cloud and DevOps practices
-
Security teams with limited time for manual testing
-
Companies that must demonstrate ongoing vulnerability management to auditors or customers
How AppCheck Fits Into Your Security Programme
Automated vulnerability scanning complements but does not replace manual penetration testing.
AppCheck provides:
-
Always-on baseline security assurance
-
Early detection between formal security assessments
-
Ongoing visibility that supports smarter testing and remediation decisions
Used together, automated scanning and expert testing create a far stronger security posture.
Start Continuous Vulnerability Scanning
If you need complete, automated security testing with real-time vulnerability coverage, AppCheck gives you the visibility required to protect your organisation, every day, not just at audit time.
Talk to CommSec about AppCheck today and gain continuous insight into your security risk.
The Differences between Penetration Testing and Vulnerability scanning
FAQ's
What is automated vulnerability scanning?
Automated vulnerability scanning is a continuous security process that automatically identifies weaknesses across applications, networks, and infrastructure. It detects known and emerging vulnerabilities without requiring manual testing, providing up-to-date visibility across your entire IT estate.
How is continuous vulnerability scanning different from one-off security tests?
One-off or periodic scans provide only a snapshot in time. Continuous vulnerability scanning runs on an ongoing basis, updating coverage as your systems change and as new vulnerabilities are disclosed, ensuring you always have current risk visibility.
What types of systems can be scanned?
Automated vulnerability scanning can cover web applications, internal and external networks, cloud environments, APIs, operating systems, and other internet-facing services. Coverage adapts as new assets are added or existing systems change.
Does automated scanning replace penetration testing?
No. Automated vulnerability scanning complements penetration testing but does not replace it. Automated scanning provides always-on baseline security coverage, while penetration testing delivers in-depth, manual analysis of complex attack paths and business logic.
How does automated vulnerability scanning help with compliance?
Continuous scanning helps organisations maintain ongoing evidence of vulnerability management for standards such as ISO 27001, PCI DSS, and GDPR. It supports compliance by demonstrating regular identification and remediation of security risks, rather than relying on point-in-time assessments.
Why Choose AppCheck?
- AppCheck is an automated online vulnerability scanner built and developed by leading penetration testers.
- Designed to run in the background searching for security flaws within your websites, applications, network and cloud infrastructure on a set schedule, whether that be out of business hours or continuously.
- Deployed as single SaaS scanning system or as part of a distributed scanning network, Appcheck offers unparalleled detection rates, accuracy and scalability.
get in touch
WHAT HAPPENS NEXT?
A member of our team will get back to you as soon as possible. They will find a suitable time to speak with you, answer any questions you have and help find the perfect solution to suit your requirements.

