Managed Vulnerability Scanning & Reporting
Optimise Your Security Posture: Elevate your cybersecurity with CheckScan+, offering continuous vulnerability scanning, expert analysis, and regular reporting. Our managed service integrates seamlessly into your SDLC, ensuring robust protection against over 100,000 CVEs and zero-day threats. Trust Ireland’s top penetration testing provider, CommSec, for in-depth reporting and dedicated support to safeguard your digital landscape.
Take the hassle out of managing your security with managed vulnerability scanning, security testing, and reporting across all environments. CheckScan+ delivers scalable, verified, and accurate reporting of each vulnerability found with the support from our security consultants (qualified and experienced SOC Analysts and Pen Testers) and delivers:
- Best in class scanning engine that tests web applications & network infrastructure
- Regular automated vulnerability scans
- Verified vulnerabilities and removal of false positives
- Regular actionable reports
- Integrate into existing SDLP and CI/CD toolset
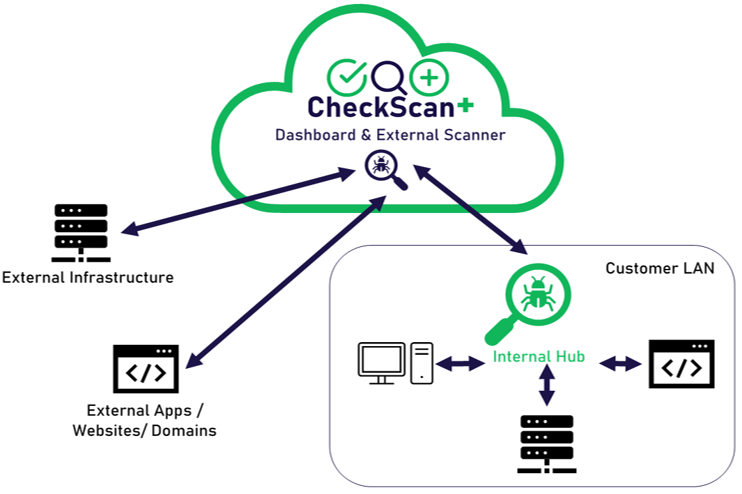
How it works?
Benefits of CheckScan+
Full management of the scanning process including scheduling, configuration and management
Full access to unlimited vulnerability scans & predefined scan templates
Removal of false positives by our security analyst team
Basic GoScript writing support if required
Full technical support from our team of qualified & experienced Security Analysts
Regular and in-depth reports that include detailed explanation of results
Vulnerability Scanning across your stack
Managed vulnerability scanning of apps, servers, cloud systems, websites, and endpoint devices, using industry-leading scanning engines.
Find vulnerabilities such as misconfigurations, missing patches, encryption weaknesses, and application bugs, including SQL Injection, Cross-Site Scripting, OWASP top 10, and more.
See for yourself. Get a free vulnerability scan and report. T&Cs apply – one free scan per company.
What makes Checkscan+different?
A lot of things, but here are the most important differences…
Platform
Take the hard work out of web app and infrastructure security testing. Our scanning platform scans for over 100,000 CVEs and zero day vulnerabilities.
Insights
The quality of our reporting cannot be matched. Our experienced security analysts gives you the clearest possible reporting and detailed explanations of vulnerabilities so you can take action where it matters.
Integration
Checkscan+ integrates with several common development tools (e.g. Azure Dev Ops, Jenkins, Jira, GitHub, etc) to integrate vulnerability scanning throughout the SDLC.

One Month Free Trial of CheckScan+
Don’t Let Vulnerabilities Cost You – Try before you buy
Cyber threats are evolving. Can you afford to ignore the vulnerabilities lurking in your systems? Try free for one month – our Managed Vulnerability Scanning Service gives you a no-risk way to:
- Uncover Hidden Weaknesses: Identify vulnerabilities before hackers do.
- Protect Your Data and Reputation: Mitigate the risk of costly breaches.
- Make Informed Decisions: Get expert recommendations for remediation.
Schedule your free scan and safeguard your business
Need a Penetration Test Instead?
CommSec is Ireland’s leading provider of penetration testing.
get in touch
WHAT HAPPENS NEXT?
A member of our team will get back to you as soon as possible. They will find a suitable time to speak with you, answer any questions you have and help find the perfect solution to suit your requirements.

